| "The Americans didn't outfight us...they out spied us!" These famous words uttered by a British commander reveal the important role of spies during the American Revolution. Reporting to General George Washington, students will travel back in time to the summer of 1781. The mission: craft a deception operation to divert the planned British attack on the incoming French fleet. Their methods: covert communication, invisible ink, and codes and ciphers. Integrating primary documents into a live- action mission, students will recreate George Washington's sympathetic stain (invisible ink), decrypt real coded messages, and attempt to save the French fleet from British attack, while American success in the War hangs in the balance!
Working on a special class project? History Day coming up? This is your opportunity to have your students dig deeper into the secret history of history. In this completely customizable opportunity, students and educators are invited to share their projects with the experts at the Spy Museum. Discovering the critical role of intelligence enables students to gain a deeper understanding of decisions, outcomes, and actions that have sometimes changed the course of history.
We can take the show on the road and offer your students a one-of-a kind experience in which they learn about the secret history of history and test their spy skills. Spy Educators will come to your school and lead a 45-minute program that will reveal the mysterious world of espionage.
|
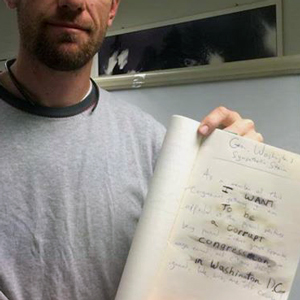
| George Washington's Sympathetic Stain Sometimes we as educators just have to pinch ourselves that we are getting paid to do some pretty cool and fun things. One such project that we recently took on was a challenge to recreate George Washington's formula for invisible ink - he called it sympathetic stain. Working with the American Heroes Channel, we filmed a segment on the spy tradecraft used during the Revolutionary War. They asked us if we could demonstrate the way in which invisible ink was created. At first, it seemed impossible, but with a bit of research (and the ability to order chemicals from the internet), we successfully recreated the secret formula! If you're interested in trying this yourself here's what you'll need: - Gallic acid (ink)
- Ferrous sulfate (revealing formula)
- A feather quill (just for effect)
- Off-white or yellowed paper
There were some other ingredients to thicken the ink and preserve it - but the above will work just fine. Try it - it's so much fun!
|
|
Quite possibly the cutest new collection item ever! Cute...but dangerous. This proof-of-concept cyber drone or Wireless, Aerial, Surveillance, Platform, was designed and built by two civilian security experts in a garage using only hand tools. Its main function is to act as an autonomous platform for hacking into wireless computer networks and cellular phone systems. Groups of hackers can log in to the drone's systems from anywhere in the world and launch attacks on computers, computer networks, and mobile devices. All a hacker needs to control the drone and its cyber payload is a laptop, tablet, smartphone, desktop, or console gaming system - anything with an internet connection. While it may look harmless, this cyber drone is a testament to what individuals outside of the military or intelligence agencies can accomplish with readily available resources, some ingenuity and skill, and knowledge of cyber operations. Come visit our first drone when it will hang in our lobby beginning late October.

 |
| | |
What makes someone decide to be a terrorist? What makes someone decide to be a spy? In the Museum’s newest mini-exhibit, you meet a man named Morten Storm who made both of those choices. Storm grew up in Denmark in a troubled home during the late 1970s. At age 13, he attempted his first armed robbery. At 16, he joined a Muslim gang. He converted to Islam and eventually became radicalized - and aspired to be a jihadist warrior. A change of heart led him to contact Danish intelligence, offering his assistance in the fight against the extremists he had once called friends. One of these friends was American-born Anwar al-Awlaki, an al Qaeda leader, considered to be the most dangerous man in the world. Storm's mission: to help CIA find al-Awlaki bring him down.
The new mini exhibit, titled Agent Storm provides a chronological glimpse into the life of Morten Storm, a rebellious youth without direction who found an identity in Islam, paving his path to extremism.

See first-hand personal artifacts from Storm that factored into his reaffirmed mission as a double agent, including passports and identification documents, burner cell phones and a series of mission notes from his clandestine activities.
The mini exhibit will remain on public display in the Museum’s lobby until March 2015 but if you don’t have time to swing by the Museum, you can share much of the exhibit’s content, videos, and artifact images with your students through the virtual exhibit.
Student discussion questions: - What is your opinion about the CIA using drones to target and kill terrorists?
- Do you think Morten Storm is a hero or a traitor? Why? Provide evidence to substantiate your opinion.
- What do you think contributed to Morten Storm’s decision to become a terrorist? What contributed to his choice to risk his life and work for the CIA?
- Do you think the CIA should award Morten Storm the $5 million prize?
Taking your students to the Spy Museum is so much more than just a fun frivolous trip. Yes, they will want to come – but that’s what makes it so great. Spying is the perfect “hook” for learning. And learning WILL happen (but deceptively, of course…they’ll never know!). Whether it’s civics, social studies, English language arts, mathematics, STEM/STEAM, art & design, or ancient to modern history and current events – we have it all and can offer hands on workshops in our private classroom to augment the visit. Just call us and we’ll help you plan for the fieldtrip of a life-time. Your curriculum….shaken AND stirred!
| |

